Certified Cyber Defender Associate
Short Courses


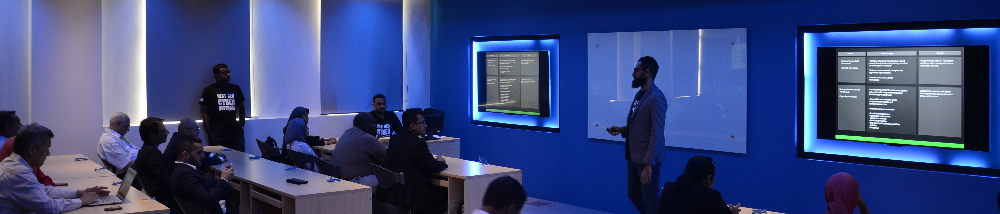
Just as every military and police force needs a firing range to hone weapons skills and battle tactics, every Next-Gen Cyber Defender needs access to a Cyber Range. Only with an Internet-scale, operationally-relevant, and ever-current Cyber Range organizations can produce the empirically valid cyber war-gaming scenarios necessary to develop IT staff skills and instincts for defensive action. Similarly, the only way to understand the resiliency of IT infrastructures is to assault every element within them using the high-stress, real-world conditions created in the controlled environment of a Cyber Range.
Our cyber security training program, Certified Cyber Defender Associate (CCDA) helps security teams build the skills necessary to defend their network against new age cyber-attacks. This program is certified by International Islamic University Malaysia (IIUM) the world’s premier Islamic University, and endorsed by CyberSecurity Malaysia, Malaysia’s national cyber security agency, under the Ministry of Science, Technology and Innovation (MOSTI).
CCDA is a 3-day beginner level training programme that provides students with a head start on understanding of fundamental Cyber Defense Concepts through hands on exposure to real-life simulated cyber-attacks. This helps build vital knowledge and skills for new age cyber defense, a much needed skill in today’s cyber landscape. Students will gain knowledge and skills in reacting to a myriad of cyber security and application traffic flows. Students will be put through Operational Scenarios that include malicious and non-malicious traffic in a safe and secure environment.
Participants of this program will develop a deep understanding and advanced skills to defend your organization and formulate defense strategies against sophisticated cyber attacks. This training program require participants to formulate defense responses using next-generation firewalls, intrusion prevention systems, URL filters, anti-spyware systems, anti-virus systems, anti-DDOS systems, data filters and file blocking systems and advanced application based protection systems. Participants will also be required to correlate information from the sources mentioned and collaborate with other team members to further develop a comprehensive cyber defense strategy.
With our cyber range program, your cyber security personnel can build the capabilities and competencies necessary to secure your organization and critical assets.